Shows

Security and Technology GuideWhat is Server Storage and Why is it Important?Modern IT infrastructure depends on the seamless integration of server and storage systems to handle complex compute workloads, ensure data persistence, and meet high availability requirements. From primary databases to email platforms, every enterprise application relies on a foundation of storage technologies designed to survive hardware failures and power cycles. In today's landscape, maximizing hardware utilization through virtualization and linking servers to centralized storage arrays via high-speed networks are essential strategies for efficient data management.The importance of these systems cannot be overstated. As organizations face increasing threats from ransomware and accidental data loss, robust backup strategies...
2026-01-1512 min
Security and Technology GuideWhat Are Cloud Solutions and How Do They Work?In the modern digital landscape, enterprises are increasingly shifting away from maintaining costly on-premises hardware and embracing the power of distributed networks. This transformation is driven by cloud solutions, a revolutionary approach to delivering computing resources, software, and virtualization capabilities on demand. At its core, cloud architecture relies on vast, centralized data centers that provide processing, storage, and networking capacity, allowing organizations to access these resources through web-based platforms.The true power of the cloud lies in its use of virtualization technology. This process abstracts physical server resources—like CPUs, memory, and storage—into isolated virtual environments. As a r...
2026-01-1412 min
Security and Technology GuideWhat is Cybersecurity and Why is Data Protection Important?In today's interconnected world, organizations face a relentless barrage of digital threats targeting their most valuable assets: their data, networks, and applications. Cybersecurity is the comprehensive practice of protecting these digital systems from attacks designed to access, alter, or destroy sensitive information. It involves establishing a robust set of technical controls and operational procedures to defend against unauthorized access, theft, and system disruption, ensuring the confidentiality, integrity, and availability of digital assets.The importance of a robust cybersecurity posture cannot be overstated. A single breach can lead to devastating financial losses, regulatory penalties, and irreparable reputational damage. An...
2026-01-1216 min
Security and Technology GuideWhat is a Network and Why is it Important?A network is a collection of interconnected devices designed to exchange data and share resources reliably. Every time you send an email, stream a video, or access a shared file, a complex system of hardware and software works in the background. Standardized communication methods, known as protocols, govern how information travels from a source to its destination, ensuring data integrity and proper delivery. The physical infrastructure handles the transmission, while processes like switching and routing determine the precise path each packet of data takes through the vast web of interconnected systems.Understanding how these networks operate is fun...
2026-01-1113 min
Security and Technology GuideHow to Choose Fire Alarm Solutions for Hotels?In the hospitality industry, guest safety is the highest priority. A hotel is a unique environment, operating 24/7 with a constant flow of transient occupants who are unfamiliar with the building's layout. This dynamic, combined with mixed-use spaces ranging from guest rooms and grand lobbies to commercial kitchens and laundry facilities, presents a complex set of challenges for fire protection. Choosing the right fire alarm system is not merely a matter of regulatory compliance; it is a critical decision that directly impacts guest safety, operational continuity, and brand reputation.The consequences of selecting the wrong system can be...
2026-01-0813 min
Security and Technology GuideWhat is Access Control? Managing Entry and SecurityModern security infrastructure has evolved far beyond the traditional lock and key. Today's facilities rely on sophisticated access control systems to manage physical entry, using electronic credentials, biometric verification, and intelligent software to protect people, assets, and sensitive information. These systems provide a robust framework for deciding who can open each door, at what time, and which areas of a building they can reach.The importance of a well-designed access control system cannot be overstated. It serves as the first line of defense, creating a secure environment by applying granular rules and policies at every entry point. By...
2026-01-0514 min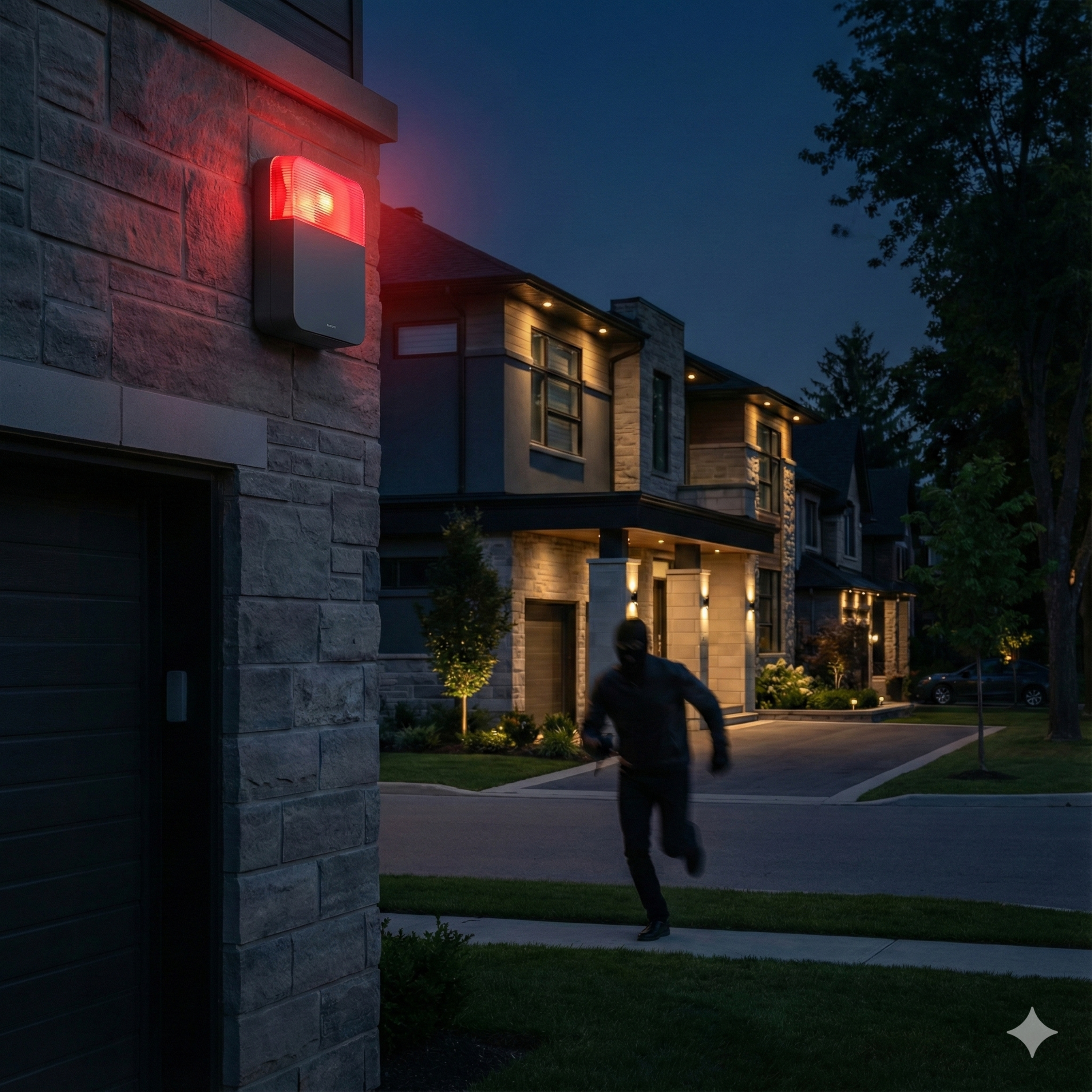
Security and Technology GuideAlarm System: Your First Line of Defense Against IntrudersAn alarm system is an integrated network of electronic devices designed to provide layered protection through intrusion detection, automated response, and continuous monitoring of secured spaces. These security systems serve as a critical first line of defense, utilizing a variety of sensors to identify burglar activity, forced entry, and other security threats before significant losses can occur. When a detection device senses unauthorized access or movement, a central control panel processes the signal and activates alerts, such as sirens, strobes, and notifications to professional monitoring centers.The importance of a well-designed alarm system cannot be overstated in...
2025-12-2113 min
Security and Technology GuideHospitality Networks: Common Design and Deployment MistakesIn the modern hospitality industry, a robust and reliable network is no longer a luxury—it is the central nervous system of the entire operation. From the moment a guest checks in using a mobile app to when they stream a 4K movie in their room, the network underpins every aspect of their experience. A high-performance hotel WiFi system enables seamless services like digital room keys, mobile ordering, and smart room controls, directly influencing guest satisfaction and operational efficiency. When the network falters, the consequences are immediate and severe, leading to negative online reviews, frustrated staff, and lost revenue.
2025-12-2012 min
Security and Technology GuideHow to Install Satellite TV in Apartment BuildingsThe installation of satellite television in apartment buildings is optimally achieved through a centralized Satellite Master Antenna Television (SMATV) system. This approach utilizes a single, shared satellite dish that feeds all individual apartments via a multiswitch and a structured coaxial cable network. Compared to allowing individual tenant dishes, a shared SMATV system offers superior aesthetic control, compliance with building codes, simplified maintenance, and more reliable signal quality.Successful implementation hinges on a meticulous planning process, including a thorough site survey to ensure an unobstructed line of sight to orbital satellites. The selection of appropriate hardware—such as di...
2025-12-1913 min
Security and Technology GuideFire Alarm Solutions for Shopping Malls and Retail ComplexesThe primary objective of a fire alarm system within a shopping mall or retail complex is to bolster life safety through rapid fire detection and the facilitation of an orderly evacuation. These high-occupancy environments present a unique risk profile, characterized by diverse tenant activities, high fire loads from merchandise, concentrated hazards in areas like food courts, and large, open spaces that can act as smoke pathways.Effective systems must adhere to stringent codes, such as NFPA 72 in the United States and EN 54 in Europe, which mandate comprehensive detector coverage, specific notification appliance standards, and deep integration with...
2025-12-1913 min
Security and Technology GuideBurglar Alarm Design for Store and Showroom SecurityEffective burglar alarm design for retail stores and showrooms is a critical component of a proactive security strategy, essential for protecting high-value inventory, cash, and staff from intrusion and theft. Unlike residential systems, retail security must account for unique challenges such as high foot traffic, multiple access points, complex operational schedules, and the specific nature of commercial threats like smash-and-grab attacks.A successful retail alarm system is built on a foundation of thorough risk assessment, which identifies vulnerable entry points and high-value zones. The core architectural principle is layered security through strategic zoning, dividing the premises into...
2025-12-1912 min
Security and Technology GuideWhat Is Emergency Evacuation and Why Is It Important?This document provides a comprehensive overview of modern emergency evacuation systems, which are critical platforms for ensuring occupant safety during crisis events. The central purpose of these systems is to coordinate alerting, communication, and the controlled movement of people away from danger. This is achieved by replacing abstract sirens with clear, intelligible voice messages delivered through integrated networks of speakers, communication pathways, and visual alerting devices.The operational core of these systems is the voice evacuation control panel, which processes inputs from fire alarms and security sensors to execute pre-programmed, scenario-specific responses. This enables sophisticated strategies like...
2025-12-1914 min
Security and Technology GuideCybersecurity in Banking and Financial ServicesCybersecurity in the banking and financial services industry is a foundational discipline essential for protecting sensitive data, preventing fraud, and maintaining customer trust in an increasingly digital landscape. The sector faces a constant and sophisticated barrage of cyber threats, including phishing, ransomware, and advanced persistent threats, which exploit expanded attack surfaces created by online banking, mobile applications, and third-party integrations.A robust cybersecurity posture is no longer merely a technical requirement but a critical business enabler and a regulatory imperative. Financial institutions must navigate a complex web of global and local regulations, such as ISO 27001, PCI DSS...
2025-12-1712 min
Security and Technology GuideUnderstanding Fire Alarm Systems: Safety FirstFire alarm systems are critical safety networks designed for the early detection of fire indicators such as smoke, heat, or flames. Their primary function is to protect building occupants by activating alerts and facilitating a coordinated emergency response. The effectiveness of these systems hinges on a coordinated, three-layered architecture: detection sensors that monitor protected spaces, a central control panel that processes signals and executes programmed logic, and notification appliances that provide audible and visual alerts for evacuation.A diverse array of detection technologies is available, each tailored to specific environmental conditions and fire risks. These range from...
2025-12-1731 min
Security and Technology GuideFacial Recognition: Who Is Watching Us and How Far They GoThis podcast synthesizes an analysis of modern surveillance, focusing on the transformative impact of facial recognition technology and the critical privacy challenges it presents. The core finding is that surveillance has evolved from passive recording to active, persistent identification, turning public and private spaces into comprehensive tracking networks. This shift is driven by CCTV analytics that extract and process sensitive biometric data, raising urgent ethical and legal questions.Under European law (GDPR), facial data is classified as special-category information, subject to the most stringent protections. Its collection and processing require a rigorous legal basis, mandatory Data Protection Impa...
2025-12-1730 min
Security and Technology GuideCCTV Surveillance Systems: Cameras, Video & SecurityModern Closed-Circuit Television (CCTV) systems have evolved from passive recording tools into a dynamic, intelligent layer of security and operational intelligence. A properly designed surveillance system is a complex integration of camera hardware, network infrastructure, video management software (VMS), and storage architecture, designed to provide complete visibility and a coordinated layer of protection across facilities. The transition from analog to IP-based architectures has been a catalyst for this evolution, enabling remote access, advanced video analytics, and seamless integration with broader security and building management platforms.Key technological pillars of a contemporary CCTV system include high-definition cameras with...
2025-12-1747 min